Palo Alto Networks Certified Cybersecurity Entry-level Technician Exam Dumps


EXAM CODE: PCCET
EXAM NAME: Palo Alto Networks Certified Cybersecurity Entry Level Technician (PCCET)
The PCCET certification is the first of its kind. It is aligned with the NIST/NICE (National Institute of Standards and Technology/National Initiative for Cybersecurity Education) workforce framework, designed to cover foundational knowledge of industry-recognized cybersecurity and network security concepts as well as various cutting-edge advancements across all Palo Alto Networks technologies.
Main Areas covered by Questions;
Fundamentals of Cybersecurity 30%
Network Security Components 30%
Cloud Technologies 20%
Elements of Security Operations 20%
Domain 1 Fundamentals of Cybersecurity 30%
Topic 1.1 Distinguish between Web 2.0 and 3.0 applications and services
Topic 1.2 Describe port-scanning methodologies and their impact
1.2.1 Nonstandard ports
1.2.2 Identify applications by their port number
Topic 1.3 Recognize applications used to circumvent port-based firewalls
Topic 1.4 Differentiate between common cloud computing service models
1.4.1 SaaS
1.4.2 PaaS
1.4.3 IaaS
Topic 1.5 Describe the business processes of supply-chain management
Topic 1.6 Describe the vulnerabilities associated with data being stored in the SaaS environment
1.6.1 Describe roles within a SaaS environment
1.6.2 Describe security controls for SaaS applications
Topic 1.7 Describe the impact of governance, regulation, and compliance
1.7.1 Differentiate between compliance and security
1.7.2 Identify major cybersecurity laws and their implications
Topic 1.8 Describe the tactics of the MITRE ATT&CK framework
1.8.1 Identify a leading indicator of a compromise
1.8.2 Describe how to use CVE
1.8.3 Describe how to use CVS
Topic 1.9 Identify the different attacker profiles and motivations
1.9.1 Describe the different value levels of the information that needs to be protected (political, financial, etc.)
Topic 1.10 Describe the different phases and events of the cyberattack lifecycle
1.10.1 Describe the purpose of command and control (C2)
Topic 1.11 Identify the characteristics, capabilities, and appropriate actions for different types of malware and ransomware
Topic 1.12 Differentiate between vulnerabilities and exploits
1.12.1 Differentiate between various business email compromise attacks
1.12.2 Identify different methodologies for social engineering
1.12.3 Identify the chain of events that result from social engineering
Topic 1.13 Identify what chain of events follows an attack
Topic 1.14 Differentiate between the functional aspects of bots and botnets
1.14.1 Describe the type of IoT devices that are part of a botnet attack
Topic 1.15 Differentiate the TCP/IP roles in DDoS attacks
1.15.1 Differentiate between DoS and DDoS
Topic 1.16 Describe advanced persistent threats
Topic 1.17 Describe risks with Wi-Fi networks
1.17.1 Differentiate between common types of Wi-Fi attacks
1.17.2 Describe how to monitor your Wi-Fi network
Topic 1.18 Describe perimeter-based network security
1.18.1 Identify the types of devices used in perimeter defense
Topic 1.19 Describe the Demilitarized Zone (DMZ)
Topic 1.20 Describe the transition from a trusted network to an untrusted network
1.20.1 Differentiate between North-South and East-West zones
Topic 1.21 Describe Zero Trust
1.21.1 Identify the benefits of the Zero Trust model
1.21.2 Identify the design principles for Zero Trust
1.21.3 Describe a microperimeter
1.21.4 Differentiate between Trust and Untrust zones
Topic 1.22 Describe the integration of services for network, endpoint, and cloud
Topic 1.23 Identify the capabilities of an effective Security Operating Platform
1.23.1 Describe the components of the Security Operating Platform
Domain 2 Network Security Components 30%
Topic 2.1 Differentiate between hubs, switches, and routers
2.1.1 Given a network diagram, Identify the icons for hubs, switches, and routers
Topic 2.2 Describe the use of VLANs
Topic 2.3 Differentiate between routed and routing protocols
Topic 2.4 Differentiate between static and dynamic routing protocols
2.4.1 Differentiate between link state and distance vector
Topic 2.5 Identify the borders of collision and broadcast domains
Topic 2.6 Differentiate between different types of area networks
2.6.1 WAN
2.6.2 LAN
Topic 2.7 Describe the advantages of SD-WAN
Topic 2.8 Describe the purpose of the Domain Name System (DNS)
2.8.1 Describe how DNS record types are used
2.8.2 Identify a fully qualified domain name (FQDN)
2.8.3 Describe the DNS hierarchy
Topic 2.9 Differentiate between categories of IoT devices
2.9.1 Identify the known security risks and solutions associated with IoT
Topic 2.10 Identify IoT connectivity technologies
Topic 2.11 Differentiate between IPv4 and IPv6 addresses
2.11.1 Describe binary-to-decimal conversion
2.11.2 Describe IPv4 CIDR notation
2.11.3 Describe IPv4 classful subnetting
2.11.4 Given a scenario, identify the proper subnet mask
2.11.5 Describe the purpose of subnetting
2.11.6 Describe the structure of IPv4 and IPv6
2.11.7 Describe the purpose of IPv4 and IPv6 addressing
Topic 2.12 Describe the purpose of a default gateway
Topic 2.13 Describe the role of NAT
Topic 2.14 Describe OSI and TCP/IP models
2.14.1 Identify the order of the layers of both OSI and TCP/IP models
2.14.2 Compare the similarities of some OSI and TCP/IP layers
2.14.3 Identify the protocols and functions of each OSI layer
Topic 2.15 Describe the data-encapsulation process
2.15.1 Describe the PDU format used at different layers
Topic 2.16 Identify the characteristics of various types of network firewalls
2.16.1 Traditional firewalls
2.16.2 Next-generation firewalls
2.16.3 Differentiate between NGFWs and traditional firewalls
Topic 2.17 Describe the application of NGFW deployment options (i.e., PA-, VM- and CN-Series)
Topic 2.18 Differentiate between intrusion detection systems and intrusion prevention systems
2.18.1 Differentiate between knowledge-based and behavior-based systems
Topic 2.19 Describe virtual private networks
2.19.1 Describe when to use VPNs
Topic 2.20 Differentiate between the different tunneling protocols
Topic 2.21 Describe the purpose of data loss prevention
2.21.1 Classify different types of data (e.g., sensitive, inappropriate)
Topic 2.22 Differentiate the various types of security functions from those that are integrated into UTM devices
Topic 2.23 Describe endpoint security standards
2.23.1 Describe the advantages of endpoint security
2.23.2 Describe host-based intrusion detection/prevention systems
2.23.3 Differentiate between signature-based and behavioral-based malware protection
2.23.4 Describe application block and allow listing
2.23.5 Describe the concepts of false-positive and false-negative alerts
2.23.6 Describe the purpose of anti-spyware software
Topic 2.24 Identify differences in managing wireless devices compared to other endpoint devices
Topic 2.25 Describe the purpose of identity and access management
2.25.1 Single- and multi-factor Authentication
2.25.2 Separation of duties and impact on privileges
2.25.3 RBAC, ABAC, DAC, and MAC
2.25.4 User profiles
Topic 2.26 Describe the integration of NGFWs with the cloud, networks, and endpoints
Topic 2.27 Describe App-ID, User-ID, and Content-ID
Topic 2.28 Describe Palo Alto Networks firewall subscription services
2.28.1 WildFire
2.28.2 URL Filtering
2.28.3 Threat Prevention
2.28.4 DNS Security
2.28.5 IoT Security
2.28.6 SD-WAN
2.28.7 Advanced Threat Prevention
2.28.8 Advanced URL Filtering
2.28.9 GlobalProtect
2.28.10 Enterprise DLP
2.28.11 SaaS Security Inline
2.28.12 Virtual Systems
Topic 2.29 Describe network security management
2.29.1 Identify the deployment modes of Panorama
2.29.2 Describe the three components of Best Practice Assessment (BPA)
Domain 3 Cloud Technologies 20%
Topic 3.1 Describe the NIST cloud service and deployment models
Topic 3.2 Recognize and list cloud security challenges
3.2.1 Describe the vulnerabilities in a shared community environment
3.2.2 Describe cloud security responsibilities
3.2.3 Describe cloud multitenancy
3.2.4 Differentiate between security tools in various cloud environments
3.2.5 Describe identity and access management controls for cloud resources
3.2.6 Describe different types of cloud security alerts and notifications
Topic 3.3 Identify the 4 Cs of cloud native security
Topic 3.4 Describe the purpose of virtualization in cloud computing
3.4.1 Describe the types of hypervisors
3.4.2 Describe characteristics of various cloud providers
3.4.3 Describe economic benefits of cloud computing and virtualization
3.4.4 Describe the security implications of virtualization
Topic 3.5 Explain the purpose of containers in application deployment
3.5.1 Differentiate containers versus virtual machines
3.5.2 Describe Container as a Service
3.5.3 Differentiate a hypervisor from a Docker Container
Topic 3.6 Describe how serverless computing is used
Topic 3.7 Describe DevOps
Topic 3.8 Describe DevSecOps
Topic 3.9 Illustrate the continuous integration/continuous delivery pipeline
Topic 3.10 Explain governance and compliance related to deployment of SaaS applications
3.10.1 Describe security compliance to protect data
3.10.2 Describe privacy regulations globally
3.10.3 Describe security compliance between local policies and SaaS applications
Topic 3.11 Describe the cost of maintaining a physical data center
Topic 3.12 Differentiate between data-center security weaknesses of traditional solutions versus cloud environments
Topic 3.13 Differentiate between east-west and north-south traffic patterns
Topic 3.14 Describe the four phases of hybrid data-center security
Topic 3.15 Describe how data centers can transform their operations incrementally
Topic 3.16 Describe the cloud-native security platform
Topic 3.17 Identify the four pillars of Prisma Cloud application security
Topic 3.18 Describe the concept of SASE
Topic 3.19 Describe the SASE layer
3.19.1 Describe sanctioned, tolerated, and unsanctioned SaaS applications
3.19.2 List how to control sanctioned SaaS usage
Topic 3.20 Describe the network-as-a-service layer
Topic 3.21 Describe how Prisma Access provides traffic protection
Topic 3.22 Describe Prisma Cloud Security Posture Management (CSPM)
Domain 4 Elements of Security Operations 20%
Topic 4.1 Describe the main elements included in the development of SOC business objectives
Topic 4.2 Describe the components of SOC business management and operations
Topic 4.3 List the six essential elements of effective security operations
Topic 4.4 Describe the four SecOps functions
4.4.1 Identify
4.4.2 Investigate
4.4.3 Mitigate
4.4.4 Improve
Topic 4.5 Describe SIEM
Topic 4.6 Describe the purpose of security orchestration, automation, and response (SOAR)
Topic 4.7 Describe the analysis tools used to detect evidence of a security compromise
Topic 4.8 Describe how to collect security data for analysis
Topic 4.9 Describe the use of analysis tools within a security operations environment
Topic 4.10 Describe the responsibilities of a security operations engineering team
Topic 4.11 Describe the Cortex platform in a security operations environment and the purpose of Cortex XDR for various endpoints
Topic 4.12 Describe how Cortex XSOAR improves security operations efficiency
Topic 4.13 Describe how Cortex Data Lake improves security operations visibility
Topic 4.14 Describe how XSIAM can be used to accelerate SOC threat response

PCCET Dumps
PCCET Braindumps
PCCET Real Questions
PCCET Practice Test
PCCET dumps free
Palo-Alto
PCCET
Palo Alto Networks Certified Cybersecurity Entry-level
Technician
http://killexams.com/pass4sure/exam-detail/PCCET
Question: 64
SecOps consists of interfaces, visibility, technology, and which other three elements? (Choose three.)
A. People
B. Accessibility
C. Processes
D. Understanding
E. Business
Answer: ACE
Question: 65
Which IoT connectivity technology is provided by satellites?
A. 4G/LTE
B. VLF
C. L-band
D. 2G/2.5G
Answer: C
Question: 66
What does Palo Alto Networks Cortex XDR do first when an endpoint is asked to run an executable?
A. run a static analysis
B. check its execution policy
C. send the executable to WildFire
D. run a dynamic analysis
Answer: B
Question: 67
What is the key to taking down a botnet?
A. prevent bots from communicating with the C2
B. install openvas software on endpoints
C. use LDAP as a directory service
D. block Docker engine software on endpoints
Answer: A
Question: 68
How does Prisma SaaS provide protection for Sanctioned SaaS applications?
A. Prisma SaaS connects to an organizations internal print and file sharing services to provide protection and sharing
visibility
B. Prisma SaaS does not provide protection for Sanctioned SaaS applications because they are secure
C. Prisma access uses Uniform Resource Locator (URL) Web categorization to provide protection and sharing
visibility
D. Prisma SaaS connects directly to sanctioned external service providers SaaS application service to provide
protection and sharing visibility
Answer: D
Question: 69
Which type of Software as a Service (SaaS) application provides business benefits, is fast to deploy, requires minimal cost
and is infinitely scalable?
A. Benign
B. Tolerated
C. Sanctioned
D. Secure
Answer: C
Question: 70
How does DevSecOps improve the Continuous Integration/Continuous Deployment (CI/CD) pipeline?
A. DevSecOps improves pipeline security by assigning the security team as the lead team for continuous deployment
B. DevSecOps ensures the pipeline has horizontal intersections for application code deployment
C. DevSecOps unites the Security team with the Development and Operations teams to integrate security into the
CI/CD pipeline
D. DevSecOps does security checking after the application code has been processed through the CI/CD pipeline
Answer: C
Question: 71
Which type of LAN technology is being displayed in the diagram?
A. Star Topology
B. Spine Leaf Topology
C. Mesh Topology
D. Bus Topology
Answer: C
Question: 72
An Administrator wants to maximize the use of a network address. The network is 192.168.6.0/24 and there are three
subnets that need to be created that can not overlap. Which subnet would you use for the network with 120 hosts?
Requirements for the three subnets:
Subnet 1: 3 host addresses -
Subnet 2: 25 host addresses -
Subnet 3: 120 host addresses -
A. 192.168.6.168/30
B. 192.168.6.0/25
C. 192.168.6.160/29
D. 192.168.6.128/27
Answer: B
Question: 73
Which two network resources does a directory service database contain? (Choose two.)
A. Services
B. /etc/shadow files
C. Users
D. Terminal shell types on endpoints
Answer: AC
Question: 74
Which model would a customer choose if they want full control over the operating system(s) running on their cloud
computing platform?
A. SaaS
B. DaaS
C. PaaS
D. IaaS
Answer: D
Question: 75
What is a key advantage and key risk in using a public cloud environment?
A. Multi-tenancy
B. Dedicated Networks
C. Dedicated Hosts
D. Multiplexing
Answer: A
For More exams visit https://killexams.com/vendors-exam-list
Kill your exam at First Attempt....Guaranteed!
Killexams has introduced Online Test Engine (OTE) that supports iPhone, iPad, Android, Windows and Mac. PCCET Online Testing system will helps you to study and practice using any device. Our OTE provide all features to help you memorize and practice test questions and answers while you are travelling or visiting somewhere. It is best to Practice PCCET Exam Questions so that you can answer all the questions asked in test center. Our Test Engine uses Questions and Answers from Actual Palo Alto Networks Certified Cybersecurity Entry-level Technician exam.
killexams.com is well-known for helping candidates pass the PCCET test on their first attempt. We have earned a high reputation among exam braindumps suppliers by maintaining quality standards, regularly updating our PCCET questions bank, and verifying the validity of our PCCET exam materials on a regular basis.
At killexams.com, we take pride in offering the latest Palo Alto Networks Certified Cybersecurity Entry-level Technician syllabus, valid and up-to-date Palo-Alto PCCET Latest Topics that are highly effective in passing the Palo Alto Networks Certified Cybersecurity Entry-level Technician exam. By choosing our platform, you can enhance your career as an expert in your industry. We have earned a reputation for assisting individuals in passing the PCCET exam on their first attempt. Our Practice Test performance has been consistently excellent over the past two years. Thanks to our PCCET Latest Topics, customers trust our Latest Topics and VCE for their actual PCCET exam. killexams.com is the leader in providing PCCET real test questions. We continuously maintain the validity and relevance of our PCCET Latest Topics to ensure that our customers succeed in the exam with high marks. Our Palo Alto Networks Certified Cybersecurity Entry-level Technician exam dumps are guaranteed to help you pass the test with flying colors. We offer our PCCET Latest Topics in two formats, PCCET PDF file, and PCCET VCE test simulator. The PCCET real exam is rapidly evolving, and we ensure that our PCCET Latest Topics is always up-to-date. You can download our PCCET Latest Topics PDF document on any device and even print it out to create your own study book. Our pass rate is high at 98.9%, and the similarity between our PCCET questions and the actual test is 98%. So, if you want to succeed in the PCCET exam on your first attempt, visit killexams.com to download our Palo-Alto PCCET real test questions.
PCCET dumps, PCCET braindumps, PCCET Questions and Answers, PCCET Practice Test, PCCET Actual Questions, Pass4sure PCCET, PCCET Practice Test, Download PCCET dumps, Free PCCET pdf, PCCET Question Bank, PCCET Real Questions, PCCET Cheat Sheet, PCCET Bootcamp, PCCET Download, PCCET VCE
Thanks to killexams.com, I no longer feel like I am taking mid-terms. Their dumps have been a great companion to me while studying for the PCCET exam. The educators have been supportive and helpful in answering all my questions, regardless of the time of day.
Richard [2023-6-2]
I recently purchased the PCCET braindump from killexams.com, and I am impressed with the updates and the fresh look of the exam. The turnaround time and support are excellent, and I highly recommend using killexams.com for exam preparation. As an average student, I was fearful of the PCCET exam as the subjects. But KE helped me succeed.
Martin Hoax [2023-4-13]
To become PCCET certified, I needed to pass the PCCET exam. I failed the exam twice before accidentally stumbling upon killexams.com through my cousin. I was very impressed by the Questions and Answers material, and it helped me secure 89% in the exam. The material was correctly formatted and enriched with essential requirements, making it easy for me to understand the concepts. I highly recommend killexams.com to anyone looking to prepare for exams.
Martin Hoax [2023-6-7]
More PCCET testimonials...

Sundry images
Palo Alto Networks, Inc. (NASDAQ:PANW) is a widespread American cybersecurity business along with three distinctive reportable segments: Product, Subscription, and aid. This analysis delves into the company's ascension to market management within the cybersecurity industry in fresh years, aiming to establish the important thing elements underlying its amazing increase in market share, via focusing on its strengths in community protection similar to protection hardware and network security utility.
Secured Cybersecurity Market management in 2022profits by using phase ($ mln) (FY Ending July)
2018
2019
2020
2021
2022
2023F
6-yr historical average
Product
880
1,096
1,064
1,one hundred twenty
1,363
1,532
growth fee % (YoY)
24.2%
24.6%
-2.9%
5.three%
21.7%
12.4%
13.1%
Subscription
758
1,033
1,405
1,899
2,539
three,393
growth fee % (YoY)
38.1%
36.2%
36.1%
35.1%
33.7%
33.6%
38.8%
assist
636
771
939
1,237
1,599
2,018
increase rate % (YoY)
27.7%
21.2%
21.8%
31.7%
29.three%
26.2%
29%
total
2,274
2,900
3,408
four,256
5,502
6,943
boom expense % (YoY)
29.5%
27.5%
17.5%
24.9%
29.3%
26.2%
26.0%
click to amplifysupply: Palo Alto, Khaveen Investments
The table above suggests Palo Alto’s phase breakdown and the 6-year standard increase for every section. in line with the enterprise’s annual file, the product section principally contains hardware and application community firewalls, the subscription section carries security software and the guide phase incorporates client support, danger researchers, and safety consultants. The product section (24.8% of complete earnings) grew 21.7% in FY2022, much stronger compared to FY2021 (5.3%) and the standard boom price (13.1%). in accordance with administration, here is as a result of
...expanded demand for our new technology of items, which contains customer transition from our legacy items. – Palo Alto Annual record
The subscription phase (forty six.1% of complete salary) grew probably the most at 33.7%, which is below its standard of 38.8%. The help segment (29.1% of complete profits) grew from 24.9% in FY2021 to 29.three% in 2022, but this is according to the usual of 29%.
For our forecast of its FY2023 revenues, we summed its Q1 to Q3 consequences for every phase and forecasted its this autumn revenues in response to its past 6-yr normal boom for every segment. universal, we see the enterprise proceed to develop decently for the entire 12 months based on its historic regular of 26%.
below, we investigate the market share increase for Palo Alto and its opponents within the cybersecurity space.
company records, Khaveen Investments
Cybersecurity salary by way of company ('CY')
2017
2018
2019
2020
2021
2022
typical
Palo Alto Networks
1,989
2,593
three,121
three,783
four,858
6,156
growth fee % (YoY)
30.4%
20.three%
21.2%
28.four%
26.7%
25.four%
Fortinet (FTNT)
1,495
1,805
2,163
2,594
3,342
4,417
increase price % (YoY)
20.7%
19.9%
19.9%
28.8%
32.2%
24.three%
Cisco (CSCO)
2,228
2,554
3,032
3,277
three,476
three,835
growth price % (YoY)
14.6%
18.7%
eight.1%
6.1%
10.3%
eleven.6%
Symantec (now referred to as Gen Digital)
four,752
4,768
2,493
2,752
3,107
increase rate % (YoY)
0.3%
-forty seven.7%
10.four%
12.9%
-6.0%
Checkpoint (CKPT)
1,855
1,917
1,995
2,065
2,167
2,330
growth cost % (YoY)
3.three%
four.1%
three.5%
four.9%
7.5%
4.7%
CrowdStrike (CRWD)
119
250
481
874
1,452
2,241
increase price % (YoY)
one hundred ten.three%
ninety two.7%
eighty one.6%
sixty six.0%
54.4%
81.0%
Microsoft (MSFT)
437
625
842
1,one hundred fifteen
1,530
2,199
boom fee % (YoY)
42.9%
34.eight%
32.4%
37.2%
forty three.8%
38.2%
IBM (IBM)
2,222
2,358
1,795
1,806
1,972
2,one hundred eighty
growth price % (YoY)
6.1%
-23.9%
0.6%
9.2%
10.5%
0.5%
Okta (OKTA)
257
399
586
835
1,300
1,858
growth expense % (YoY)
fifty five.7%
46.8%
forty two.5%
fifty five.7%
forty two.9%
48.7%
trend Micro (OTCPK:TMICF)
1,321
1,464
1,520
1,686
1,654
1,705
increase expense % (YoY)
10.eight%
3.9%
10.9%
-1.9%
3.1%
5.four%
Zscaler (ZS)
154
243
360
536
860
1,348
boom expense % (YoY)
fifty seven.5%
48.2%
48.eight%
60.four%
fifty six.8%
fifty four.3%
Others
21,486
17,667
22,845
30,621
36,035
39,721
growth expense % (YoY)
-17.eight%
29.three%
34.0%
17.7%
10.2%
14.7%
total
33,561
36,629
43,511
fifty one,687
61,399
71,a hundred
increase price % (YoY)
9.1%
18.eight%
18.8%
18.eight%
15.8%
sixteen.3%
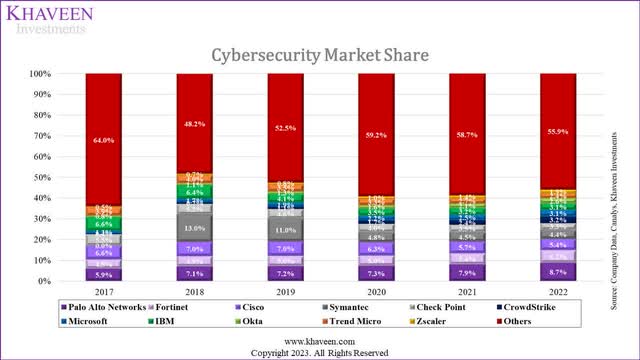
click to amplifysupply: business statistics, Canalys, Khaveen Investments
We derived the market share through taking the security revenues for each business divided through the dimension of the whole cybersecurity market offered by Canalys, from 2017 to 2022. In 2017, Palo Alto had a 5.9% market share, behind Cisco (6.6%) and IBM (6.6%), but then had continual share increase and took the first spot in 2022 with an 8.7% market share. both Cisco and IBM normally misplaced market share, ending with 5.4% and three.1% respectively. Fortinet grew from 4.5% in 2017 to six.2% in 2022 whereas Checkpoint misplaced market share, beginning with 5.5% and ending with three.3%.
searching at the boom rates, Palo Alto has the optimum 5-year general growth rate (25.4%) amongst the good 5 organizations in terms of market share, with Fortinet (24.3%), Cisco (eleven.6%), Symantec (-6.0%) and Checkpoint (4.7%) following behind.
Cybersecurity Market Segments
section dimension ($ bln) (2022)
segment size (2027F)
CAGR
identification & entry administration
14.7
27.9
13.7%
Vulnerability & security Analytics
13.9
29.5
sixteen.2%
statistics safety
4.2
12.3
23.9%
net & e-mail safety
3.9
7.2
12.eight%
network safety
22.9
forty two.3
13.0%
Endpoint security
9.4
23.four
20.0%
integrated possibility administration
10.9
21.2
14.three%
complete
eighty.0
163.8
15.four%
click to enlargesource: Canalys, Gartner, Market.Us, MarketsandMarkets (security Analytics), MarketsandMarkets (information security), MMR, Fortune business Insights, Radicati community, MarketsandMarkets (built-in risk administration)
We derived our personal cybersecurity market breakdown from Canalys and Gartner. We introduced the integrated possibility management phase that changed into in Gartner’s breakdown to the Canalys breakdown as it was absent in Canalys and it represented Palo Alto’s risk Intelligence & safety Consulting phase. We got the segment size and CAGR for the cybersecurity segments from a few analysis websites comparable to MarketsandMarkets, Fortune business Insights, and Market.us. Of the seven cybersecurity market segments, we recognized that network security is certainly the largest section at $22.9 bln, followed via identity & entry management ($14.7 bln) and Vulnerability & security Analytics ($13.9 bln). The optimum-growing segments are facts protection (23.9%), Endpoint safety (20%), and Vulnerability & comfortable Analytics (sixteen.2%).
Palo Alto breaks down its cybersecurity services into four areas which can be network safety (comprises security access provider edge), Cloud security, security Operations, and risk Intelligence & protection Consulting. When searching at the company’s annual record, investor displays and company website, we see that the items from these four areas cowl all seven cybersecurity market segments.
youngsters Palo Alto does not deliver a earnings breakdown in terms of the 4 areas that it operates in, it cited inside its 2021 analyst day presentation that the community safety salary for FY21 was $three.7 bln, which represented 87% of total income for FY21. for this reason, 87% of Palo Alto’s profits comes from one market phase (community safety), whereas the final 13% of earnings comes from the closing six segments.
based on Forbes, the business’s key competitors are Fortinet and Checkpoint in the community safety market phase. also, Palo Alto and Fortinet lead network protection with over 20% market share each. The three competitors mentioned are also part of the precise 5 agencies by way of market share, which indicates network security is the greatest and most sought-after market section via security vendors.
however network security has the biggest section dimension, its CAGR is lessen than that of the entire CAGR. regardless of the low section boom, Palo Alto has nevertheless been in a position to benefit massive market share with network safety as it represents 87% of the company’s income which is mind-blowing. in addition, Palo Alto’s good two rivals, Fortinet and Cisco, offer products in the identical areas as Palo Alto in terms of community protection, Cloud protection, safety Operations, and risk Intelligence & safety Consulting. Yet, Palo Alto’s extraordinary efficiency allowed it to gain market share and upward thrust to become the market leader. In conclusion, Palo Alto has the highest market share in the cybersecurity market as a result of its dominance in community security and we additional investigate under even if the company has a aggressive potential over its rivals with the aid of examining each the hardware and application aspect of the enterprise.
security Hardware Market chiefin this part, we analyze the hardware facet of Palo Alto’s company. in response to the annual document, the utility side has a wide array of items, whereas hardware is made up of its physical community Firewalls.
A network Firewall is a safety device used to keep away from or restrict unlawful entry to private networks by using policies defining the handiest traffic allowed on the network; some other site visitors searching for to join is blocked. – Palo Alto
during this segment, we appear into the protection hardware market and verify if Palo Alto has a aggressive potential in protection hardware.
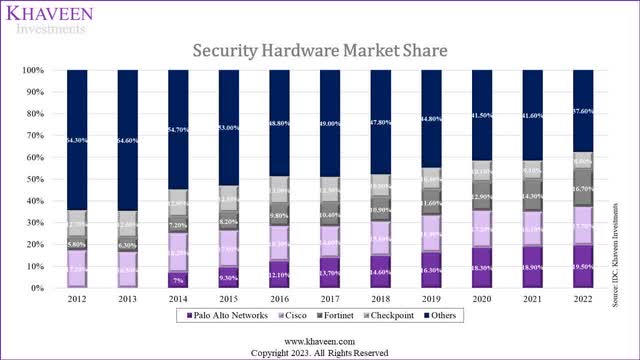
IDC, Khaveen Investments
The chart above indicates the safety appliance market share until 2022. Palo Alto had a 7% share in 2014 however became the market leader with a 19.5% share in 2022. nonetheless, Cisco's share had been pretty good with 17.7% in 2022. yet another massive gainer turned into Fortinet, which had a 5.eight% share and climbed to a sixteen.7% market share. Checkpoint’s share declined from 12.7% to 8.5%.
From the chart above, the largest gainers had been Palo Alto and Fortinet, with a minor change of simplest between both. in addition, we observed a research file published with the aid of Miercom that compares Palo Alto and Fortinet firewall hardware to show that Palo Alto is the superior player in the safety hardware area. The verify turned into run on three different network firewall products from each and every company and “company environments have been simulated and challenged with true-world traffic eventualities to give an accurate assessment of product performance”. The products chosen have been to replicate what purchasers, in small organizations and records centers, can predict in terms of performance.
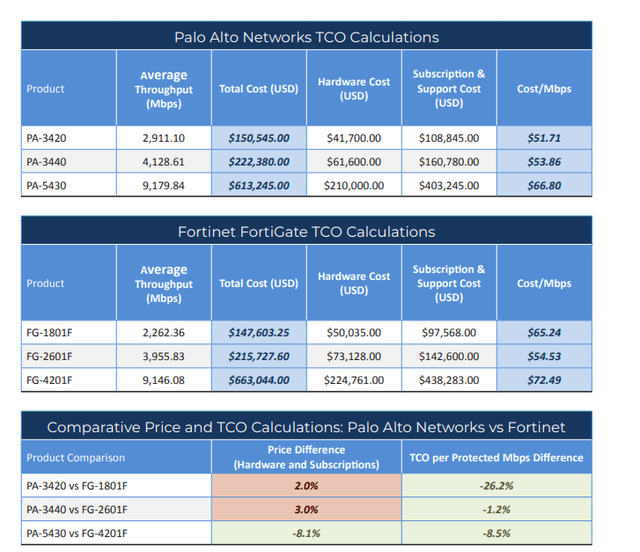
Miercom
overall, the main goal was to discover the normal throughput and TCO (total cost of ownership) per Mbps assessment for the three sets of items. Throughput refers back to the “volume of facts efficiently transmitted over a connection”. TCO per protected Mbps refers to the cost-benefit cost for each and every product which is derived by using taking complete charge divided by average throughput. relating to the effects, Palo Alto’s community firewall hardware is much sophisticated in comparison to that of Fortinet’s as the commonplace throughput is greater for all three Palo Alto items and the charge per Mbps is reduce for all three Palo Alto products.
In conclusion, Palo Alto has a significant aggressive advantage over its opponents in the security hardware space as recognized in its community firewall hardware efficiency evaluation with Fortinet. Its aggressive capabilities is additionally reflected via its management position in the safety hardware market (19.5% market share).
network protection utility Market chiefduring this area, we analyze Palo Alto’s network safety application and how it compares with opponents during this space. When taking a look at Palo Alto’s community protection competition, we recognized that community Firewalls and comfy entry carrier part (SASE) had been common sub-segments among the many groups.
To examine performance, we seemed into the newest Gartner Magic Quadrants for every of those items to see if Palo Alto has an capabilities in the network safety utility area. despite the fact we couldn't attain a quadrant for SASE, we obtained the quadrants for SSE and SD-WAN which can be subsets of SASE. in keeping with Palo Alto, SSE “gives the protection service aspects of a comprehensive SASE (reported “sassy”) method”. furthermore, Palo Alto brought up that SD-WAN...
...allows businesses to securely join clients, applications, and information throughout distinct places whereas featuring enhanced efficiency, reliability, and scalability. - Palo Alto
it is exceptionally advantageous for firms that have far off work. in keeping with its recent profits, the company’s administration highlighted its energy because the most effective business to be categorized as a frontrunner in each SSE and SD-WAN through Gartner.
This apart from our leadership position in SD-WAN, makes us the most effective SASE vendor in the industry to be named a leader in the Gartner SSE and SD-WAN Magic Quadrants. - Nikesh Arora, Chairman & CEO
in the chart under, the first quadrant to the left is the network firewall quadrant, the 2nd one is the protection service side quadrant and the third is the SD-WAN quadrant. it will also be mentioned that the community firewall quadrant includes hardware.
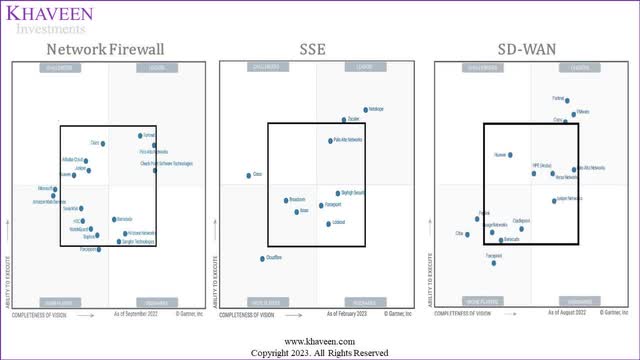
Gartner, Netskope, Palo Alto, Khaveen Investments
We compared a complete of seven groups, with 4 being the biggest community security rivals (Palo Alto, Cisco, Fortinet, Checkpoint) and the last three being corporations that appeared in additional than one quadrant (Juniper, Barracuda, Forcepoint). To achieve a ranking for every of the seven companies we derived our own scoring equipment. The scoring device is as follows:
Rank
score
formula
1
a hundred
proper correct quadrant, past black square
2
70
exact correct quadrant, inside black square
3
50
precise left and bottom correct quadrants
four
30
backside left quadrant, within black square
5
20
bottom left quadrant, beyond black square
0
10
now not inside any quadrants
click to amplifysource: Khaveen Investments
hence, the closer the enterprise is to a rank of one, the better the rating and the enhanced its performance for that product. the whole rating for each and every business is as follows:
business
community Firewall
SSE
SD-WAN
score
Palo Alto
2
2
2
210
Cisco
3
3
1
200
Fortinet
2
0
1
a hundred and seventy
Juniper (JNPR)
3
0
3
a hundred
Forcepoint
5
3
5
90
Barracuda
three
0
4
eighty
Checkpoint
2
0
0
70
click on to amplifysupply: Gartner, Netskope, Palo Alto, Khaveen Investments
by searching on the quadrants, we believed that Palo Alto may be the market chief for community security utility, the rating gadget extra supports our declare with Palo Alto having the highest total ranking (210) amongst the seven corporations. however, Cisco has a complete score of 200 which is extraordinarily near Palo Alto. both axes for the Gartner magic quadrants are "the capacity to execute" and "the completeness of imaginative and prescient". Having the highest rank indicates that typical, Palo Alto is the ultimate for these two metrics.
probably the most methods Gartner measures a firm’s capacity to execute is by means of its product capabilities, the fiscal success of the specific product, the seller’s skill to adapt to market changes, customer experience, and the dealer’s potential to satisfy dreams and commitments. Palo Alto’s skill to execute is mirrored via its client base with ninety five% of Fortune a hundred organizations using its items and services. Its means to adapt to market alterations is reflected with the aid of the increase in predominant product releases over the last three years, with 22 (FY20), 29 (FY21),49 (FY22), and already 35 within the first half of FY23.
moreover, Gartner measures a firm’s completeness of vision with the aid of its market realizing, advertising, and income approach. Palo Alto’s market realizing is mirrored through sixty six% of clients the usage of three or extra of its network security services as of FY 21 There has also been a swift upward push in the variety of money owed with a worth of $1 mln and above, going from 542 in FY19 to 921 in FY21.
In conclusion, Palo Alto has a aggressive talents in community security software, albeit not large as a result of Cisco’s excessive rating from Gartner’s magic quadrants. Palo Alto’s competitive competencies is considered by way of having 95% of Fortune a hundred groups as purchasers, increasing variety of product releases, move-promoting items to valued clientele and the boost in gigantic price debts.
chance: Low community safety Market boomdespite the fact Palo Alto has had fast boom in market share over the last few years, it has principally been pushed by way of the community protection section (25.4% 5-year normal). although, the expected market increase of 13% is the 2d lowest growth rate amongst the six cybersecurity market segments. youngsters Palo Alto has security Operations (Endpoint safety) and cloud safety (a mixture of a number of cybersecurity market segments) which can be excessive-growth segments anticipated to develop at 20% and 26.eight% respectively, the earnings share of those segments must raise if Palo Alto is to keep its competitive skills within the long term. nonetheless, Palo Alto is all of a sudden innovating in these segments which is seen when evaluating its new product releases in FY21 in comparison to FY22. The product releases within the security operations segment extended from 9 to 18, the cloud protection segment rose from 6 to 13 whereas network safety had a minor boost from 14 to 18 new product releases. We accept as true with this shows that Palo Alto is beginning to focus on bigger boom segments.
VerdictPalo Alto Valuation
FY2024F
profits ($ mln)
8,842
P/S
8.50x
equity value ($ mln)
seventy five,159
Shares outstanding ('mln')
305.9
cost goal ($)
245.seventy four
existing price ($)
213.39
Upside
15.sixteen%
click to magnifysupply: Palo Alto, Khaveen Investments
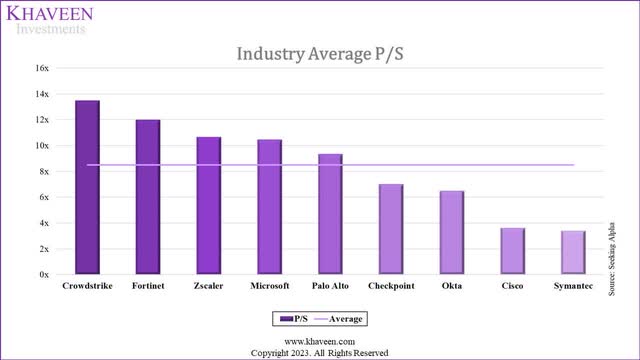
We forecasted Palo Alto’s revenues for FY2024 based on its past 6-12 months commonplace growth fee for the product, subscription, and guide segments and derived complete revenues of $8.eighty four bln. We valued the company with a P/S valuation as we forecasted it to have a excessive boom fee above 20% for 2024. We based the ordinary P/S ratio on nine cybersecurity corporations that are eight.50x. The agencies that have been chosen are Symantec, Cisco, Okta, Checkpoint, Palo Alto, Microsoft, Zscaler, Fortinet, and CrowdStrike.
in the hunt for Alpha, Khaveen Investments
In our evaluation, we followed that Palo Alto Networks skilled a surprising boost in market share, positioning itself because the leading player within the cybersecurity market through the end of 2022. We attribute this success to the enterprise's competitive part, certainly within the construction of safety hardware and software segments. specially, we identified that Palo Alto's community firewalls surpassed opponents, which we accept as true with contributed to its dominance in protection hardware. moreover, Palo Alto stood out because the sole leader in a variety of community protection software sub-segments, where we decided that it boasted the maximum average score amongst its competitors during this segment, which bills for 87% of its income in FY2021. These findings affirm our belief in Palo Alto's competitive capabilities over its rivals. based on our P/S valuation, we assign a purchase rating to the business, with a target cost of $245.70.
Palo Alto Networks Certified Cybersecurity Entry-level Technician Free PDF
Palo Alto Networks Certified Cybersecurity Entry-level Technician braindumps
Palo Alto Networks Certified Cybersecurity Entry-level Technician PDF Questions
Palo Alto Networks Certified Cybersecurity Entry-level Technician PDF Braindumps
Palo Alto Networks Certified Cybersecurity Entry-level Technician PDF Braindumps
Palo Alto Networks Certified Cybersecurity Entry-level Technician exam dumps
Palo Alto Networks Certified Cybersecurity Entry-level Technician Free Exam PDF
I see the PCCET page showing new date but questions are unchanged. Why?
Killexams.com keep on checking update on regular basis and change the exam questions accordingly. If PCCET questions in your download section are already up to date, the system changes the PCCET exam update date. But if any new update is received, it is included in the question bank and users are informed by email to re-download the exam files. Killexams overwrites the previous files in the download section so that you have the latest exam questions all the time. So, there is no need to search the update anywhere. Just re-download the exam files if you receive an intimation of update.
Yes, Killexams is completely legit and also fully well-performing. There are several includes that makes killexams.com traditional and authentic. It provides up-to-date and 100 % valid exam dumps formulated with real exams questions and answers. Price is really low as compared to almost all the services online. The questions and answers are current on normal basis utilizing most recent brain dumps. Killexams account arrangement and device delivery is amazingly fast. Data downloading is certainly unlimited and also fast. Help is available via Livechat and E-mail. These are the features that makes killexams.com a sturdy website that provide exam dumps with real exams questions.
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Latest Questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician learn
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician information source
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician real questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Exam Braindumps
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician PDF Questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician outline
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Latest Questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician exam
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Cheatsheet
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Practice Questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician tricks
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician dumps
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician study help
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Free PDF
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Exam Questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician study help
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician information source
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Exam Questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Study Guide
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician boot camp
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician study help
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Exam Cram
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician study tips
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician test
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician learning
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician study help
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician braindumps
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician dumps
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician real questions
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician dumps
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician techniques
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Practice Test
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician exam success
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician Dumps
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician PDF Download
PCCET - Palo Alto Networks Certified Cybersecurity Entry-level Technician real questions
There are several Questions and Answers provider in the market claiming that they provide Real Exam Questions, Braindumps, Practice Tests, Study Guides, cheat sheet and many other names, but most of them are re-sellers that do not update their contents frequently. Killexams.com is best website of Year 2023 that understands the issue candidates face when they spend their time studying obsolete contents taken from free pdf download sites or reseller sites. That is why killexams update Exam Questions and Answers with the same frequency as they are updated in Real Test. Exam Dumps provided by killexams.com are Reliable, Up-to-date and validated by Certified Professionals. They maintain Question Bank of valid Questions that is kept up-to-date by checking update on daily basis.
If you want to Pass your Exam Fast with improvement in your knowledge about latest course contents and topics, We recommend to Download PDF Exam Questions from killexams.com and get ready for actual exam. When you feel that you should register for Premium Version, Just choose visit killexams.com and register, you will receive your Username/Password in your Email within 5 to 10 minutes. All the future updates and changes in Questions and Answers will be provided in your Download Account. You can download Premium Exam Dumps files as many times as you want, There is no limit.
Killexams.com has provided VCE Practice Test Software to Practice your Exam by Taking Test Frequently. It asks the Real Exam Questions and Marks Your Progress. You can take test as many times as you want. There is no limit. It will make your test prep very fast and effective. When you start getting 100% Marks with complete Pool of Questions, you will be ready to take Actual Test. Go register for Test in Test Center and Enjoy your Success.
Below are some important links for test taking candidates
Medical Exams
Financial Exams
Language Exams
Entrance Tests
Healthcare Exams
Quality Assurance Exams
Project Management Exams
Teacher Qualification Exams
Banking Exams
Request an Exam
Search Any Exam